To store cultural media without losing control, understand the fundamentals of data sovereignty—keeping your data within specific legal borders and ensuring proper metadata management. Choose storage solutions that support strict access controls, security measures like encryption, and clear rights management. Engage communities early and respect indigenous protocols to protect ownership. By planning for long-term preservation and compliance, you can maintain control and preserve cultural integrity—continue exploring how to master these essential steps.
Key Takeaways
- Store cultural media within borders to ensure compliance with local laws and preserve data sovereignty.
- Use detailed metadata to maintain cultural context and protect sensitive information.
- Engage with indigenous communities early to obtain permissions and respect ownership rights.
- Implement strong access controls and digital rights management to prevent unauthorized use.
- Regularly update security protocols and backups to ensure long-term preservation and control.

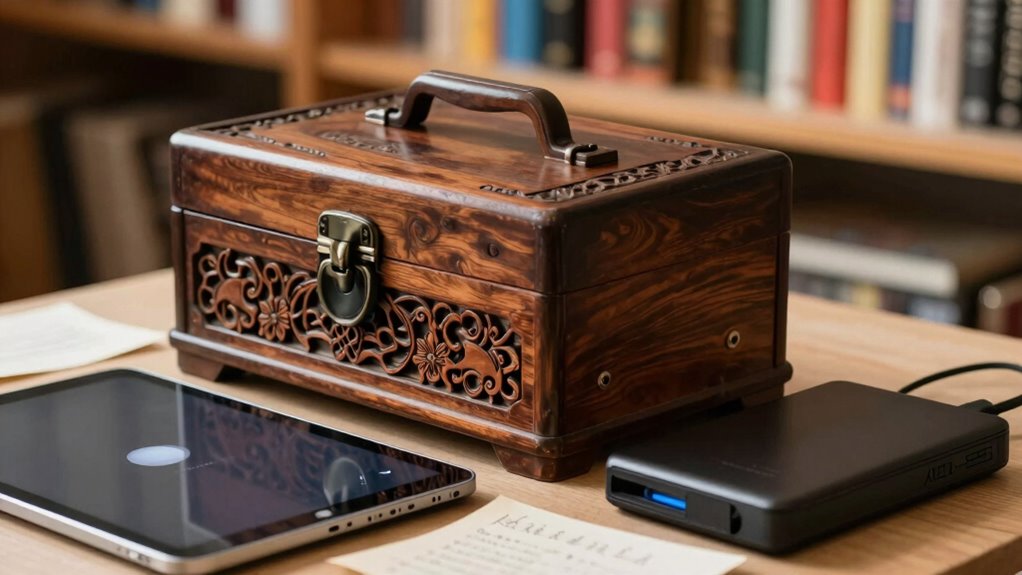
Apricorn 2TB Aegis Padlock USB 3.0 256-Bit AES XTS Hardware Encrypted Portable External Hard Drive (A25-3PL256-2000)
Hardware encrypted drive
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
What Is Data Sovereignty and Why Is It Key for Cultural Media?
Data sovereignty refers to the idea that digital data is subject to the laws and regulations of the country where it is stored or processed. For cultural media, this means respecting local regulations while maintaining cultural authenticity. Proper metadata management helps you organize and protect sensitive information, ensuring that cultural details are accurately represented and accessible. When data stays within specific borders, you reduce risks of misinterpretation or loss of context that could compromise authenticity. This control allows you to preserve the integrity of cultural media, ensuring it reflects its true origins. Understanding data localization empowers you to navigate legal requirements effectively while safeguarding the cultural significance embedded in your digital assets. Additionally, implementing compliance measures ensures your data practices align with regional legal frameworks, further protecting your cultural content. Recognizing the importance of contrast ratio can also help in maintaining the visual fidelity of digital representations of cultural media, ensuring images remain true to their original appearance. Moreover, being aware of regional data laws assists content creators in avoiding legal pitfalls and ensuring their cultural media remains compliant across different jurisdictions. Incorporating data management best practices further enhances your ability to control and secure your digital cultural assets, fostering trust and authenticity across borders. It’s essential for maintaining trust and authenticity across borders.

The DAM Book
Used Book in Good Condition
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Unique Challenges of Storing Cultural Media Across Borders

Storing cultural media across borders presents unique challenges because legal frameworks and regulations vary widely between countries. Cross border storage requires understanding diverse legal requirements that protect cultural diversity while respecting sovereignty. You might face restrictions on data transfer, differing privacy laws, or specific cultural content regulations. These rules can complicate access, sharing, and preservation efforts, especially when managing media from multiple regions. Ensuring compliance means balancing the need to honor cultural diversity with legal obligations. Additionally, geopolitical tensions or restrictions can hinder storage solutions or create uncertainty around data control. Orchestrating these complexities demands careful planning and awareness of international laws to prevent loss of access or control over culturally significant media stored across borders. Legal compliance is critical to navigate these complex international regulations effectively. Developing a thorough understanding of data sovereignty principles can help organizations better align their storage strategies with cross-border data management requirements and cultural sensitivities. Recognizing the importance of cultural media preservation is essential for maintaining the integrity and accessibility of diverse cultural expressions globally. Furthermore, understanding the role of international treaties can facilitate smoother cooperation and data sharing across jurisdictions.

The DAM Book
Used Book in Good Condition
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
How to Choose Storage Solutions That Keep You in Control

Choosing the right storage solutions is essential to maintaining control over your cultural media, especially when operating across borders. Focus on options that support robust metadata management, enabling you to organize, categorize, and locate your media efficiently. Effective metadata helps preserve context and cultural significance while simplifying access controls. Additionally, prioritize solutions with strong user authentication features to ensure only authorized individuals can access or modify your media. This is crucial for enforcing your rights and preventing unauthorized use. Opt for platforms that give you clear control over storage location, data privacy, and security protocols. By combining precise metadata management with reliable user authentication, you guarantee your cultural media remains protected and manageable, no matter where it’s stored or accessed. Moreover, understanding content management systems can help you select storage options tailored to different types of media, ensuring optimal organization and preservation. Considering data sovereignty is also critical to ensure your media remains within jurisdictions aligned with your legal and cultural requirements, and choosing providers that support data localization can further reinforce this control. Clarifying your ownership rights ensures that your media is properly protected according to your legal and cultural standards.
secure cloud storage for cultural media
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Controlling Access and Managing Rights for Your Cultural Media

To protect your cultural media, you need to control who can access it and how rights are managed. Implementing access controls and establishing clear policies make sure only authorized people use your assets appropriately. Digital rights management tools can help enforce these policies and prevent unauthorized use. Additionally, choosing reliable smart lock systems can enhance physical security for your digital assets and storage spaces. A combination of physical and digital security measures is essential for comprehensive content protection. Maintaining transparency about your affiliate relationships can also build trust with your audience and ensure ethical sharing of your media. Being aware of privacy policies and how data is handled further supports the responsible management of your media assets. Incorporating security best practices ensures that both digital and physical assets are safeguarded against potential threats.
Implementing Access Controls Effectively
Implementing access controls effectively is essential for safeguarding your cultural media and ensuring that only authorized individuals can view or modify it. By setting up strong access controls and user authentication, you prevent unauthorized access and protect your valuable assets. Use role-based permissions to assign appropriate rights, and regularly review access logs to monitor activity. Consider the following table to help prioritize your controls:
| Control Type | Example Implementation |
|---|---|
| User Authentication | Multi-factor authentication for all users |
| Role Management | Assign roles based on responsibilities |
| Permission Settings | Limit editing rights to trusted personnel |
| Access Auditing | Log and review access events |
| Regular Updates | Keep access controls current and secure |
Focusing on these strategies guarantees your cultural media remains secure and under your control. Ensuring your controls adapt to changing security threats is crucial for maintaining ongoing protection. Incorporating strong access controls and regularly reviewing permissions are vital steps in maintaining control over your media assets. Regularly updating your security protocols helps address emerging vulnerabilities and keeps your media protected.
Establishing Clear Rights Policies
Establishing clear rights policies is essential for controlling access and effectively managing your cultural media. You need to define who owns the rights, how media can be used, and under what conditions. Proper metadata management helps you track rights details, usage restrictions, and licensing terms, making it easier to enforce policies. Implementing robust user authentication ensures only authorized individuals can access sensitive or restricted content. Clear policies prevent unauthorized sharing or misuse, protect cultural integrity, and support compliance with legal requirements. Regularly update your rights policies to reflect changes in ownership, licensing, or cultural considerations. By combining precise metadata management with strict user authentication, you create a secure framework that preserves your media’s integrity and guarantees your control over access and rights remains uncompromised.
Utilizing Digital Rights Management
Building on your rights policies and metadata management, Digital Rights Management (DRM) tools offer a practical way to control access and enforce usage restrictions on your cultural media. By implementing digital watermarking, you embed invisible identifiers into your content, helping trace unauthorized distribution and proving ownership. Metadata tagging plays a vital role by attaching detailed information about rights, restrictions, and licensing terms directly to your files. These combined techniques allow you to specify who can view, copy, or share your media and under what conditions. DRM systems can automate enforcement, ensuring your cultural media remains protected according to your policies. Ultimately, utilizing digital watermarking and metadata tagging within DRM helps you maintain control over your cultural assets and safeguard their integrity.
Navigating Legal Rules and Respecting Cultural Ownership

Moving through legal rules and respecting cultural ownership require careful attention to both national regulations and indigenous perspectives. You must understand how cultural metadata is used to describe and categorize media, guaranteeing it accurately reflects the community’s values and context. Respecting indigenous protocols means engaging with communities early, obtaining proper permissions, and honoring their guidelines for cultural expression. Laws may vary across jurisdictions, so familiarize yourself with local and international legal frameworks that govern cultural media. By integrating cultural metadata thoughtfully, you help preserve the authenticity and integrity of the media. Prioritize transparent communication and genuine partnerships with indigenous groups to ensure their ownership rights are upheld. This approach fosters trust, respects cultural sovereignty, and keeps you aligned with legal and ethical standards.
Protecting Your Media With Encryption and Security Measures

To safeguard your media, you need to understand different encryption algorithms and how they secure your data. Implementing multi-layered security strategies helps defend against evolving threats, while regular security audits ensure your defenses stay strong. Staying proactive with these measures is essential to safeguard your information effectively.
Encryption Algorithms and Types
Have you ever wondered how your private data stays secure even when transmitted across the internet? It all comes down to encryption algorithms, which transform your information into unreadable code. There are different types of encryption, such as symmetric and asymmetric encryption. Symmetric encryption uses one key for both encrypting and decrypting data, making it fast but requiring secure key sharing. Asymmetric encryption employs a pair of keys—a public key for encryption and a private key for decryption—enhancing security during transmission. Choosing the right encryption algorithm depends on your needs, balancing speed and security. By understanding these types of encryption, you can better protect your cultural media from unauthorized access, ensuring your data remains under your control and sovereignty.
Multi-Layered Security Strategies
Implementing multiple security measures creates a robust defense for your media, ensuring that your data remains protected from unauthorized access. To strengthen your strategy, consider these steps:
- Use encryption alongside metadata management to control and track data access efficiently.
- Apply data anonymization techniques to remove personally identifiable information, reducing exposure risks.
- Combine strong access controls with encryption keys to limit who can view or modify your media.
- Regularly update security protocols to address emerging threats and vulnerabilities.
Regular Security Audits
Regular security audits are essential for maintaining the integrity of your media protections and ensuring your encryption and security measures remain effective. As you undergo cloud migration, vulnerabilities can emerge, making audits crucial to identify and address gaps early. These audits help verify that your security protocols comply with vendor requirements and industry standards, ensuring vendor compliance. Regular checks also ensure that encryption remains robust and that access controls are properly enforced. By routinely reviewing your security posture, you can detect potential threats before they escalate, protect sensitive cultural media, and maintain sovereignty over your data. Staying proactive with security audits not only strengthens your defenses but also demonstrates your commitment to safeguarding your media in an ever-evolving digital landscape.
Planning Long-Term Preservation and Access Strategies

Planning long-term preservation and access strategies is essential to guarantee that data remains secure, accessible, and usable over time. To do this effectively, you should focus on establishing solid preservation workflows that incorporate regularly updated archival metadata. This ensures your digital media stays organized and discoverable. Consider these key points:
- Define clear preservation workflows to maintain data integrity.
- Use exhaustive archival metadata for easy retrieval and context.
- Regularly test backups to prevent data loss.
- Plan for technological changes that may affect access.
Developing a Sustainable Approach to Cultural Media Ownership

To guarantee cultural media remains accessible and meaningful over time, developing a sustainable approach to ownership is essential. You should focus on fostering community collaboration, ensuring local voices guide decisions about media management. This approach helps preserve cultural authenticity, so the media reflects the community’s true identity and values. By involving community members, you create shared responsibility, reducing reliance on external entities and promoting long-term stewardship. It’s also important to implement flexible policies that adapt to changing needs and technologies. Building partnerships with cultural institutions or indigenous groups can strengthen ownership rights and maintain control. Prioritizing transparency and respecting cultural protocols ensures that media remains a genuine representation of the community, supporting its preservation and relevance for future generations.
Frequently Asked Questions
How Does Data Sovereignty Impact Indigenous Cultural Media Rights?
Data sovereignty directly impacts your indigenous cultural media rights by ensuring you maintain control over digital preservation and protect cultural autonomy. When data is stored within your jurisdiction, you can set policies that respect your community’s values and prevent unauthorized access. This empowers you to safeguard sacred media, uphold traditional knowledge, and retain authority over how your cultural expressions are shared and preserved globally.
What Are the Costs Associated With Implementing Sovereignty-Focused Storage Solutions?
They say, “You get what you pay for,” and implementing sovereignty-focused storage solutions isn’t cheap. You’ll face initial investments in specialized storage infrastructure and ongoing compliance costs to meet legal and cultural standards. These expenses can add up quickly, but they guarantee your cultural media remains under your control. While costly, this approach protects your rights and preserves your heritage, making the investment worthwhile in the long run.
Can International Treaties Influence Cultural Media Data Sovereignty?
International treaties can substantially influence your cultural media data sovereignty by shaping digital borders and legal frameworks. They establish agreements that may require you to store data in specific jurisdictions or comply with foreign regulations, potentially limiting your control over the data. You need to stay informed about these treaties, as they can both expand and restrict your ability to manage cultural media within your own terms, affecting sovereignty and compliance.
How Do Technological Advancements Affect Control Over Stored Media?
Ever wondered if technology can help you keep control? With advancements like cloud storage and encryption techniques, you can protect your cultural media more effectively. These tools allow you to store data remotely while maintaining access and security. Are you leveraging the latest tech to prevent unauthorized access? Embracing these innovations means you stay in charge, even as technology evolves, ensuring your cultural media remains protected and under your control.
What Role Do Local Communities Play in Managing Cultural Media Sovereignty?
You play a crucial role in managing cultural media sovereignty through community engagement and enhancing digital literacy. By actively involving local communities, you guarantee their voices shape how cultural media is stored and shared. Promoting digital literacy empowers them to take control, make informed decisions, and protect their cultural heritage in digital spaces. Your efforts help maintain cultural integrity while fostering a sense of ownership and control over their media.
Conclusion
Did you know that over 80% of cultural media stored internationally faces risks like loss or unauthorized access? By understanding data sovereignty and choosing the right storage solutions, you can keep control of your cultural assets. Protecting your media with encryption and respecting legal boundaries are key steps. With a sustainable, long-term plan, you’ll ensure your cultural stories remain secure and accessible for generations to come. Take control today and safeguard your cultural legacy.









